Web Application Security: Top 11 Best Practices for 2021
Last Updated on July 24, 2023 by Editorial Team
Author(s): Sophia Martin
Originally published on Towards AI.

Do you know cybercrime or hacking is quickly becoming more profitable than an illegal drug trade? Yes, you read it right! Every year we see thousands of hacking and security breaching cases in the news in which companies face monetary losses as well as it also spoils their brand reputation.
Have a look at some facts about cybercrime:
- In the year 2019, IoT (internet of things) devices became significant targets for malware attacks. (source)
- Email spam is one of the most common methods for cyber-criminals to spread malware. (source)
- The external network connecting smart homes makes the UK, US, and China more vulnerable to cyber-attacks. (source)
- Roughly 1 out of 5 files are not protected. (source)
- Users in the United States open around 1 in 3 phishing emails. (source)
- Information or data loss accounts for 43% of the costs in the cyber-attacks. (source)
- More than half of Millennials have experienced cybercrime in the year 2019. (source)
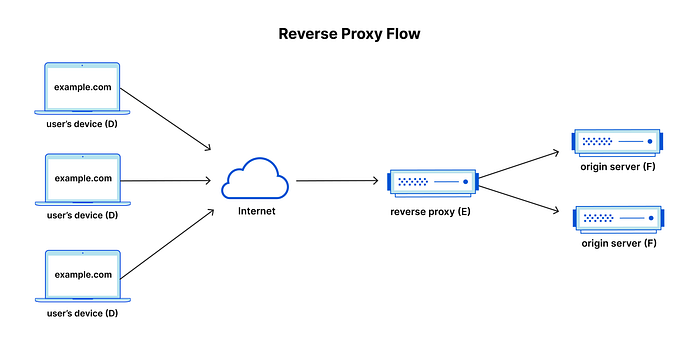
It is clear from these stats that data or information security is a considerable risk in any organization. Here is an infographic depicting the importance of website security:


So, what are the steps for securing your website? Let’s find out in this blog:
1. Always Back-up All Your Website Data
When a malware infection or security breach occurs, and you need to restore your web app after that, it would be disastrous not to store the updated or recent version of your website. When the time comes to live your website again, you will be glad you postponed it. Therefore return your data as much as possible. It is worth noting that most of the hosting service providers will provide backups from their servers if this mishappening happens.
2. Periodically Scan your Website for Vulnerabilities
Security scans and checks should be done regularly to stay on top of the security of your web application. It would be a wise decision to do security scans on your websites at least once every week. In addition to this, you should scan after every change that you have made in your web application.
It is worth noting that various security scanners, even experienced people, will not be able to detect all the security issues. Scanners are either pattern-based or heuristic, and malware is always engineered to be invisible from the scanners. Some security scanners find malware better than others, and on the other hand, some struggle with false positives. Most of the security scanners do not work at all. Moreover, you should still learn about various security flaws & weaknesses.
3. Use a Website Security Platform Like WebARX
WebARX is one of the best tools for monitoring and protection, especially for web app developers. You may be thinking about why developers? Because with the help of WebARX, you can quickly secure your entire client portfolio and protect as many websites as you like.
So you can protect your web applications, save money and time, and stand ahead in the competition (it is always a good practice to add ‘Protected by WebARX’ to the website).
What does WebARX platform include:
WebARX is a web application firewall (WAF) that has a ton of features, and some of the features are:
OWASP (Open Web Application Security Project) base rules: it provides everyday protection for websites.
Smart threat intelligence that monitors your domain’s mentions in various hacker forums, defacement databases and target lists.
Blocking protection that is automated for different malicious traffic, brute-force attacks, and public exploit attacks.
Stats and logs on their cloud-based dashboard for checking up regularly
Defacement, uptime, and blacklist monitoring
State of art software vulnerability monitoring
Security reports about every site
2-factor authentication
Alert integrations for Slack & mail
The WebARX tool can be used on all PHP based web applications, and the prices are quite attractive as well. In addition to this, you can contact any software development company and have your own customized website security platform for better protection from hackers.
4. Conduct website security awareness training within your organization
If you run a business, there are chances that only a few people within your company have a decent understanding of the web application security importance and how it works. Most of the users in your organization have the most basic understanding of this issue, and it can make them even careless. In addition to this, it is also problematic because uneducated users fail to identify various security risks.
By educating your staff and employees, they’ll weaken themselves more easily. Furthermore, speeding up all about web application security is one of the best ways to get everyone in the act of finding and removing various security vulnerabilities. With this in mind, you can consider bringing in a web application security specialist in order to conduct various awareness training for your employees.
By getting all your staff and employee on board and making sure they know what to do if they encounter any software security vulnerability or any other problems, you can strengthen the overall security of your web application development process and get the best possible security
5. Effectively strategize your remediation operations
In recent years, software breach has been on the rise, spiking drastically in the year 2019 when the count was more than doubled from the previous year. This particular trend of software vulnerability shows no signs of giving up anytime soon, which means when you hire a web development company, you have to keep this thing in your mind.
Therefore, to effectively weed out any security flaws in your web apps, you should do a threat assessment which is based on the severity of a vulnerability (CVSS rating), which is how effective your web application is to your actions and other factors. In addition to this, when it comes to open source vulnerabilities, it helps to comprehend if your proprietary code is actually using any weak functionality in a given open source component.
Moreover, if the functionality of an unsafe component is not receiving any calls from your software product, it is considered ineffective; therefore, not a high risk, even if it has a severe rating of CVSS. A smart strategy prioritizes pressure apprehensions in the first place, taking into account various factors at play, and subsequently leaves those at comparatively low risk.
6. Effectively encrypt all your crucial website data
Making encryption of all your data provides you mental peace that your information is safe from hackers and cybercriminals. Then he locked you in danger of falling sensitive traffic information through man-in-the-middle attacks and other forms of intrusion. The IDs and the passwords for the user or other sources of information If you might be endangered treasurest up unto thyself against them, to explain to the country of the future by the text of customers.
If encryption so that it includes all your basic checklist that you are accompanied by a certificate SSL. But now it has become standard HTTPS, and would not be left behind. Hashing friends and being useful. Also, that “It is Crypto does not develop,” he said. Dedicated security team, which will have the right to have her.
7. Manage privileges of your website
All of your organization’s who do not have access to everything. Application security best practices, as well as network security leadership, which encourages us to limit access to only need it.
This is double. The first is that if a hacker can pop in accounting documents, Bob, we would like to be given later to roam freely on sensitive. The second, at other times of the latter, generally in insider threats. In order to avoid abominableness such a character, the white men held that it follows from the principal unless the users work, and the work that they must do the briefing with his. While this can be an act in itself, it may not be necessary, and it is also a good way to fear.
8. Embrace automation to effectively manage the vulnerabilities
Recent applications have a lot of developers who have had their safety in recent years, especially when it comes to vulnerability to business management. Although this transfer of responsibility seems to be the right move, data requires knowledge of its proximity to address vulnerabilities of the code development process for developers is now more than ever challenging.
Since the year 2017, a growing number of weaknesses, as was stated in the notes to make strategic Upcharikrn ops. Given the scale, to force developers to multipliers are automated tools to help maintain the number of alerts that will come your way.
Developers in the past a few years, they are the way to the automated DevOps to be standard when the sun also confirms this. Recently, many companies are trying to secure inclusion in its Dielsi, thus Award for Devsecops squad.
At this point, it can be to change the Ops of the war, helps to avoid the flight of ‘tear, And of sorrows, that there shall come in the sight of release, to try them.
The trial of proprietary code developed during the offer by the Security Application (SAST) can help you find potential vulnerabilities in your code. While this can be affordable to play a role in the security of the blockage of the legs with water, and proprietary code, except it, be so great in the aspect of the overall codebase. If there had not been explored with the open-source automated vulnerability management and security issues for commissioning, we are able to do so.
9. Effectively track all your assets
There is a very famous “you cannot protect what you do not know you have.” Did you not know that these duties as servers or applications to use? If you are using open source components that are in various web apps?
Just go Equifax, the protection of which is the lack of information on the late will be fined $700 for the more than 145 million people, ten times, it is important to be more fun than to remember and what does not run software that the apps. And the face of the credit rating agency had failed when it could be barely distinguished client vulnerable to patch up the open-source Apache struts-in components web portals, and it is believed that they were unaware that it is used.
In addition to the memory of the disaster of your head or of the good things to come. Now you can help them to keep the path of the just is right, after all. For this reason, he advises that it will be an automated process to feel that it is like a Sisyphean task organization to continue its growth. While you are at, it will take time for the kinds of things that are known to be of great importance gifts, and lesser importance and varied. Will serve to remedy this, and then the risk is your judgment.
10. Perform a threat assessment
The need for security, which is already suffering, we must begin to know and how to reduce them. They are able to freely make use of the power to burst in the use of things, who, a moment? Do we have current security measures to prevent or detect this attack? What does it not require other instruments?
These are the questions that are asked while going for the threat assessment, if not even the peril to the sum involved. However, this would out have realistic expectations for the expectation of the things which we can not accomplish this mission safely. This means that even though we may think of us as the maximum level of security, nothing is ever possible. I do not think there is a need for a certain rule and measure, both to be worthy, our horses, which we have a long, actually the last one. Pushing many signs can be safely ignored. Remember that security is a marathon, not a sprint.
It is granted that you can not risk the probability formula x = result of the first attack risk. The other way to think of evil is not so, the case, that it is more probable that if the verses of poetry. The chances of a whale, for it, would be to rub a little of the heavens if any evil. Alternatively, a hike through the bites of mosquitoes, therefore, is to try to get enough to be annoying, it is likely that at the end of the world.
11. Stay on top of your security patching
You patch up the latest versions of your operating system? What about the third-party software? Chances are, you are next. But the question is how do you explain yourself?
Maintains projects such as patches and updates with commercial or open-source software vendors to his city, one of the most important steps you can take to ensure the security of its software. Furthermore, because they were searched by security vulnerability researchers and reported to them by their product or project planning and security as well as public consumption database published in the National Vulnerability Database (NVD) is. Ideally, it created a fix before publication and is pushed out, which gives users the chance to secure in their software.
Of course, if he did this, the lakes would not be available, the more the assurance of safety to the highest step of the way in which we had not. That said, this kind of updating your application to be at the top of the security if the best practice on the day of the week.
Let’s Wrap Up:
In this blog, we have seen various points that you need to follow if you want to enhance the security level of your website. A vulnerable website can be detrimental to any organization. It can impact you in terms of monetary loss as well as reputation loss. You can hire a web development company that follows all crucial security checklists before delivering you the website. In addition to this, you can also take the above-mentioned measures to protect your web applications from hackers.
Join thousands of data leaders on the AI newsletter. Join over 80,000 subscribers and keep up to date with the latest developments in AI. From research to projects and ideas. If you are building an AI startup, an AI-related product, or a service, we invite you to consider becoming a sponsor.
Published via Towards AI
Towards AI Academy
We Build Enterprise-Grade AI. We'll Teach You to Master It Too.
15 engineers. 100,000+ students. Towards AI Academy teaches what actually survives production.
Start free — no commitment:
→ 6-Day Agentic AI Engineering Email Guide — one practical lesson per day
→ Agents Architecture Cheatsheet — 3 years of architecture decisions in 6 pages
Our courses:
→ AI Engineering Certification — 90+ lessons from project selection to deployed product. The most comprehensive practical LLM course out there.
→ Agent Engineering Course — Hands on with production agent architectures, memory, routing, and eval frameworks — built from real enterprise engagements.
→ AI for Work — Understand, evaluate, and apply AI for complex work tasks.
Note: Article content contains the views of the contributing authors and not Towards AI.