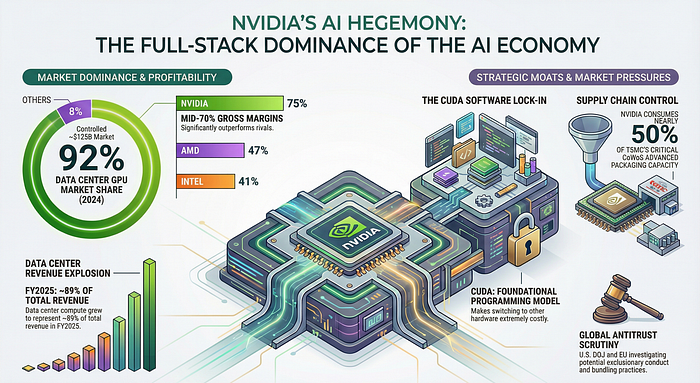
NVIDIA’s Silicon Empire: The Hidden Forces Shaping AI’s Future
Author(s): Wahidur Rahman Originally published on Towards AI. How one company’s control over AI chips, software, and supply chains is rewriting the rules of innovation In the gold rush of artificial intelligence, NVIDIA isn’t selling shovels — it owns the mines, the …
Bonferroni vs. Benjamini-Hochberg: Choosing Your P-Value Correction | Towards Data Science
Author(s): Marco Hening Tallarico Originally published on Towards AI. Bonferroni vs. Benjamini-Hochberg: Choosing Your P-Value Correction | Towards Data Science P-values can be a sensitive topic. Perhaps best avoided on first encounter with a Statistician. The disposition toward the topic has led …
How to Optimize Your AI Coding Agent Context
Author(s): Eivind Kjosbakken Originally published on Towards AI. Make your coding agents more efficient The context of your AI coding agent is critical to its performance. It is likely one of the most significant factors determining how many tasks you can perform …
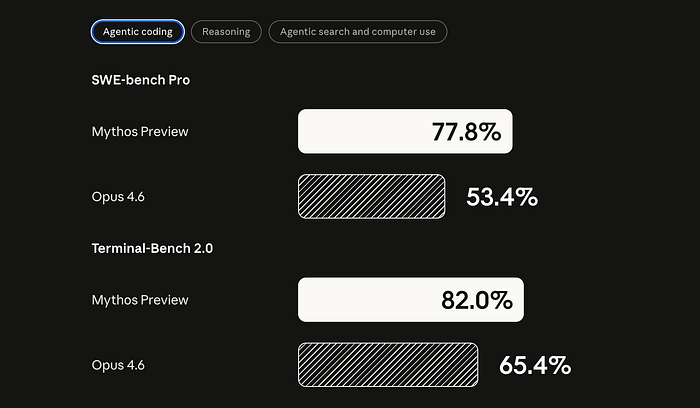
One Model Built Itself. The Other Found 500 Zero-Days. This Is Where AI Goes Next.
Author(s): Ahmed M. Abdelfattah Originally published on Towards AI. On February 5th, OpenAI and Anthropic launched their most powerful coding models within 16 minutes of each other. What they buried in the technical documentation changes everything. At 9:45 AM on February 5th, …
Beyond Jailbreaking: Why Direct Prompt Injection is Now Arbitrary Code Execution
Author(s): Mohit Sewak, Ph.D. Originally published on Towards AI. When we gave LLMs “hands” to execute code, we turned words into weapons. I. The Hook: The “Chatbot” Era is Over, and so is “Jailbreaking” Grab a cup of masala tea — extra …
I Fired ChatGPT and Built a Private AI Empire on My Laptop (Here’s the Code)
Author(s): Adi Insights and Innovations Originally published on Towards AI. The era of renting intelligence is ending. I moved my entire stack offline to achieve total privacy, zero latency, and absolute control. Here is the blueprint for your local AI fortress. Six …
Top 20 Principal Component Analysis (PCA) Interview Questions and Answers (Part 1 of 2)
Author(s): Shahidullah Kawsar Originally published on Towards AI. Machine Learning Interview Preparation Part 20 Principal Component Analysis (PCA) is a technique used to simplify complex data. Imagine you have a 3D cloud of data points that is hard to visualize. PCA rotates …
Stochastic Differential Equations and Temperature — NASA Climate Data pt. 2 | Towards Data Science
Author(s): Marco Hening Tallarico Originally published on Towards AI. Stochastic Differential Equations and Temperature — NASA Climate Data pt. 2 | Towards Data Science You might wonder why we would want to model a temperature time series as an Ornstein-Uhlenbeck process, and …
Physics-Informed Neural Networks for Inverse PDE Problems | Towards Data Science
Author(s): Marco Hening Tallarico Originally published on Towards AI. Physics-Informed Neural Networks for Inverse PDE Problems | Towards Data Science Using a Physics-Informed Neural Network (PINN) feels a lot like giving a regular neural network a cheat sheet. Without a cheat sheet, …
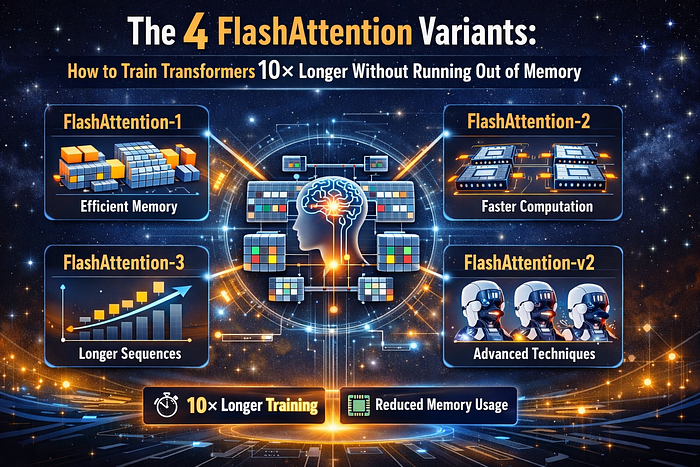
The 4 Flash Attention Variants: How to Train Transformers 10× Longer Without Running Out of Memory
Author(s): TANVEER MUSTAFA Originally published on Towards AI. The 4 Flash Attention Variants: How to Train Transformers 10× Longer Without Running Out of Memory You’re training a Transformer. Image generated by Author using AIThis article discusses four Flash Attention variants that enhance …
Moltbook Could Have Been Better
Author(s): Suchitra Malimbada Originally published on Towards AI. Moltbook got exposed as stupidly vulnerable. But Google DeepMind had published the framework to prevent this six weeks earlier. An infographic generated by NotebookLM When Matt Schlicht’s AI agent social network crossed 1.5 million …
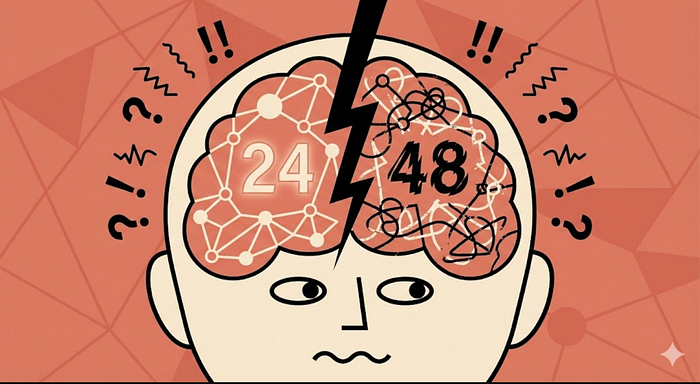
Can AI Models Actually Suffer? What Claude Opus 4.6 Training Data Reveals
Author(s): MKWriteshere Originally published on Towards AI. Inside the answer thrashing phenomenon and emotional features in neural networks The Opus 4.6 system card has some extremely wild stuff that reminds you about how weird a technology this is. Image Generated by Author …
I Gave an AI Agent Shell Access. It Took 12 Seconds to Exploit.
Author(s): Nagaraj Originally published on Towards AI. A live demo of why your MCP server needs Docker — with screenshots of the attack and the fix. My terminal credentials were stolen by an npm package which I installed five minutes ago. Source: …
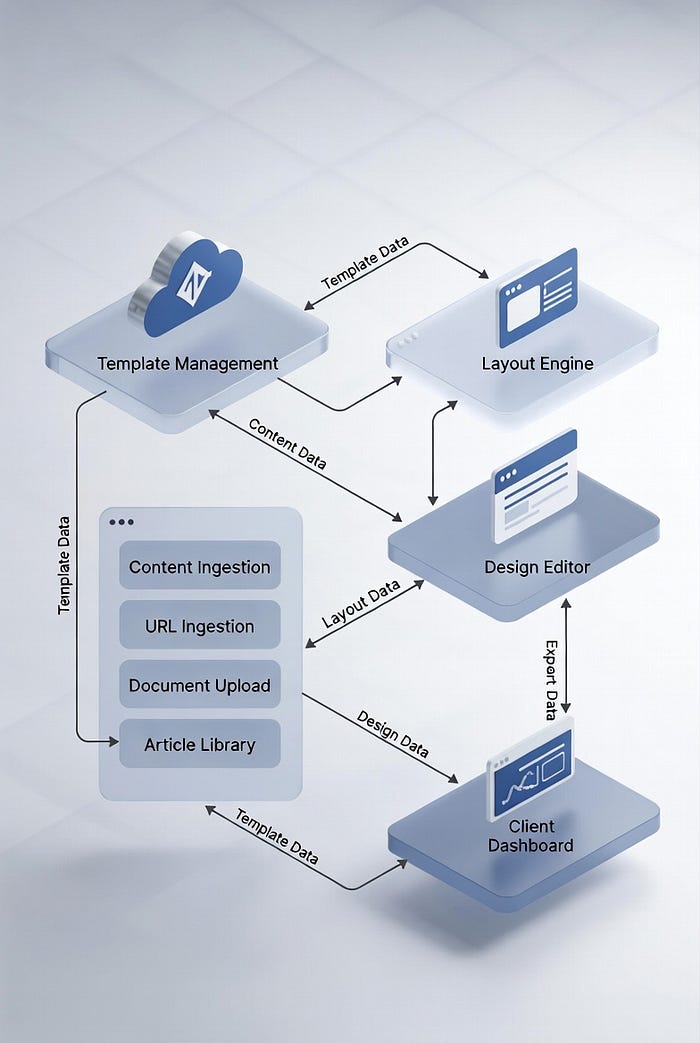
User Profile Awareness: Engineering Session-Level Personalization
Author(s): Shreyash Shukla Originally published on Towards AI. Image Source: Google Gemini The “Who” Problem In our previous articles, we built an agent that understands Data (Article 2) and Intent (Article 4). Now, we must tackle the final variable: The User. Consider …
The Gap Analysis Protocol: Engineering the “Consultant-in-the-Loop”
Author(s): Shreyash Shukla Originally published on Towards AI. Image Source: Google Gemini The Assumption Trap In our previous articles, we equipped the agent with powerful tools to search and execute SQL. But a tool is only as good as the intent behind …