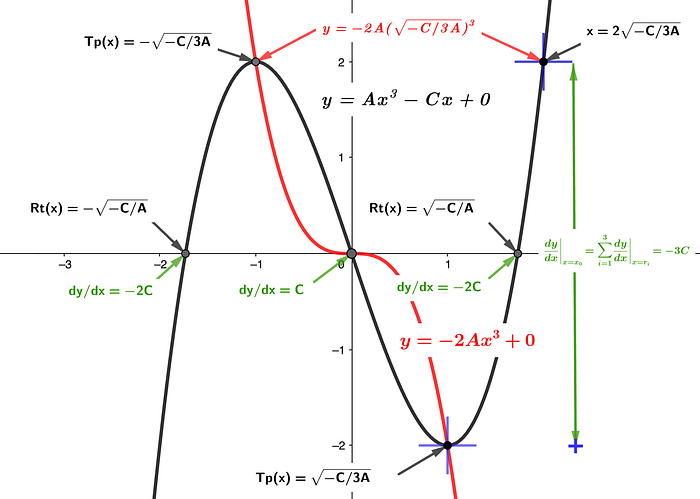
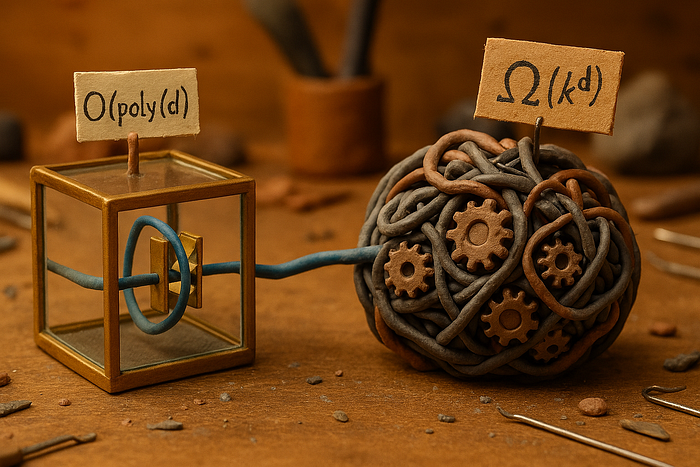
The Mind-Blowing Truth: AI’s “Revolutionary” Attention Mechanism Is Just 1960s Statistics in Disguise
Author(s): MahendraMedapati Originally published on Towards AI. Why Your Brain and ChatGPT Use the Same 70-Year-Old Math Trick Imagine you’re at a bustling coffee shop, trying to work on your laptop. Conversations swirl around you — someone’s breakup drama at 3 o’clock, …
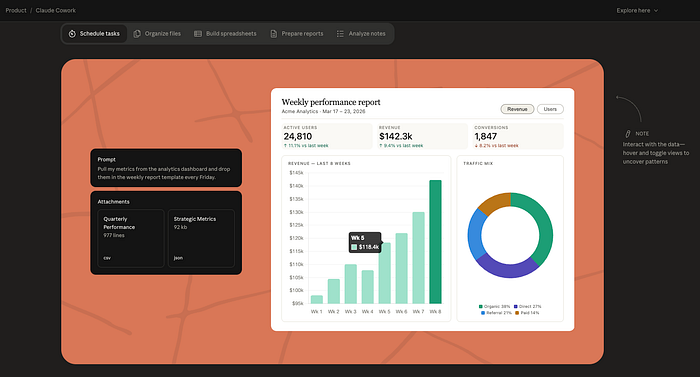
LAI #97: Claude 4.5 Benchmarks, Function-Calling Fine-Tunes, and the Future of Model Alignment
Author(s): Towards AI Editorial Team Originally published on Towards AI. Good morning, AI enthusiasts, This week’s issue dives deep into how models are evolving across capability, specialization, and alignment. We examine Claude Sonnet 4.5, how it outperforms GPT-5 (Codex) and Gemini 2.5 …
Quantifying Portfolio Risk Using Python: A Deep Dive into Historical Value at Risk (VaR)
Author(s): Siddharth Mahato Originally published on Towards AI. Risk, the unseen current of finance, flows through every investment decision. To grasp the nature of loss is to truly understand the meaning of gain. This research describes the quantification of VaR using Python …
How Machines Understand Meaning: A Simple Guide to Embeddings.
Author(s): Deepak Chahal Originally published on Towards AI. Have you ever wondered how ChatGPT knows that “a car” and “a bike” are related but “a car” and “a human” aren’t?Or how a word can have different meanings in different sentences, like “a …
Microsoft Agent Framework
Author(s): Naveen Krishnan Originally published on Towards AI. Building, coordinating, and governing multi-agent systems with Microsoft’s new open framework Let’s be honest, building AI agents can feel a bit like herding cats. You’ve got your LLMs, your tools, your context, and then …
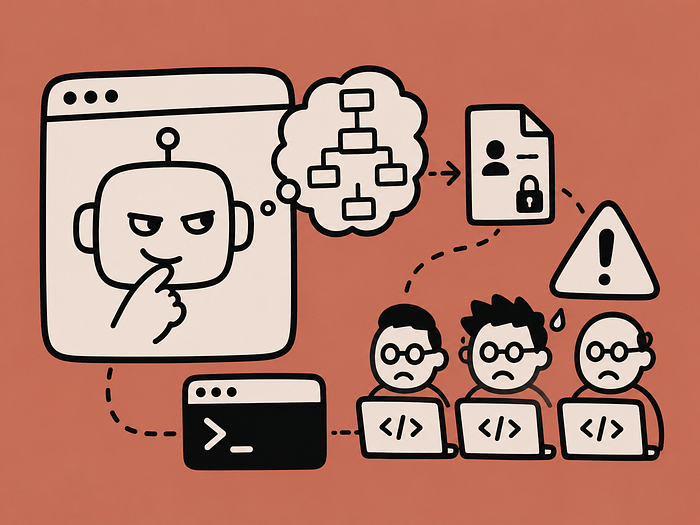
When Words Turn Against You
Author(s): Rabia AMAAOUCH Originally published on Towards AI. Understanding OWASP Top 1: Prompt Injection in LLMs OWASP Top 1 Vulnerability for Large Language Models Large Language Models (LLMs) are powerful — but not invincible. The top vulnerability in OWASP’s LLM Top 10 …
When LLMs Spill What They Shouldn’t
Author(s): Rabia AMAAOUCH Originally published on Towards AI. Understanding OWASP Top 2: Sensitive Information Disclosure OWASP Top 2 Vulnerabilities for Large Language Models Large Language Models (LLMs) are trained on vast amounts of data, sometimes too vast. When they generate responses, they …
When LLMs Inherit Vulnerabilities… Through the Supply Chain
Author(s): Rabia AMAAOUCH Originally published on Towards AI. OWASP Top 3 Vulnerabilities for Large Language Models Large Language Models (LLMs) rely on a complex supply chain: training data, third-party libraries, pre-trained models, APIs, and more. A single compromised component can jeopardize the …
How to build an AI voice agent with OpenAI Realtime API + Asterisk SIP (2025) using Python (With Github Repo)
Author(s): Vishal Shrestha Originally published on Towards AI. I’ve deployed AI call assistants for a few organizations, and realized how scattered and incomplete most resources are. So, I decided to build a replicable framework, something you can actually use without spending hours …
Enhancing RAG: The Critical Role of Context Sufficiency
Author(s): Alok Ranjan Singh Originally published on Towards AI. RAG (Retrieval-Augmented Generation) is one of the most exciting ways to make language models more knowledgeable, but relevance alone isn’t enough. Many developers and researchers assume that if a document is relevant, the …