The Great Bifurcation: How Hardware Root-of-Trust Determines Whether AI Leads to Reality or Illusion
Last Updated on February 19, 2026 by Editorial Team
Author(s): Simplified Complexity
Originally published on Towards AI.
As the world teeters between a verifiable “Reality” and a synthetic “Illusion,” the difference lies in the silicon. Here is why the United Kingdom’s legal and engineering heritage mandates a shift toward Hardware Root of Trust for the autonomous age.

The imagery of society standing at a fork in the road is timeless, but rarely has it been as technically stark as it is today. We are on the cusp of the autonomous age — an era where AI agents, IoT devices, and Web3 protocols will execute complex tasks without constant human intervention.
A recent, profound sentiment circulating on social media captured this moment perfectly. It described a choice between two futures: a “Reality” path, characterized by a utopian, Net Zero world where autonomous agents built via human authority serve to free workers; and an “Illusion” path, a landscape of suffering, spoofing, and a 100x fold increase in Sybil attacks, where fake AI scripts masquerade as autonomous agents, creating an unaccountable “influencer and consumer society.”
This is not merely philosophical speculation. This bifurcation is a direct consequence of engineering decisions we are making right now. The difference between these two futures comes down to a single, critical architectural paradigm: whether we anchor digital intelligence to a Hardware Root of Trust (RoT), or allow it to exist as detached, floatings software.
The Path to Illusion: The Dangers of Detached Software
To understand the “Illusion” path, we must understand the inherent weakness of pure software in an autonomous system.
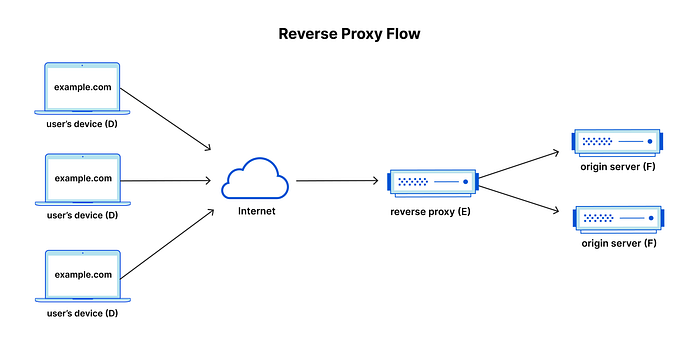
In the digital realm, software is infinitely reproducible. An AI agent defined solely by code, lacking a unique physical anchor, has no verifiable identity. If I can copy the code for an “autonomous agent,” I can spin up ten thousand instances of it instantly.
This vulnerability leads directly to the dystopian vision outlined in the “Illusion” scenario:
1. The Sybil Attack Nightmare: In computer security, a Sybil attack occurs when a single adversary controls multiple fake identities to gain disproportionate influence. In a world of purely software-based AI, Sybil attacks become trivial and devastatingly scalable.
Imagine an economy reliant on autonomous agents for voting in Decentralised Autonomous Organisations (DAOs), verifying news, or managing supply chains. Without hardware anchoring, a bad actor can deploy millions of “fake AI scripts pretending to be agentic,” flooding the network with noise, spoofed votes, or fraudulent transactions. This creates the “illusion economy,” where metrics are faked, influence is bought via bot farms, and reality is obfuscated by synthetic noise.
2. The Erosion of Accountability: When a purely software-based agent causes harm — perhaps via a flash crash in a financial market or a critical failure in cyber-physical infrastructure — attributing blame is impossible. The software can be deleted, wiped, or spun up elsewhere under a new guise. This directly mirrors the concern that societal catastrophes are blamed on script no one is responsible [for]. Without a physical identity, there is no legal or moral accountability chain.
The Path to Reality: Anchoring Autonomy with Hardware Root-of-Trust
The “Reality” path, leading to the idealised Web3 world where autonomous agents genuinely serve humans, requires execution environments that are verifiable and immutable. This is only achieved through a Hardware Root-of-Trust.
A Hardware RoT is a set of functions within the physical silicon of a device — like a Trusted Platform Module (TPM 2.0), a Secure Enclave, or ARM TrustZone technology — that is inherently trusted. It cannot be modified by software. It provides a unique, cryptographic identity burned into the chip itself.
How does this hardware anchor translate to the utopian vision of “Reality”?
1. Verifiable Agentic Identities (True Web3): If every autonomous AI agent operates within a secure hardware enclave, its actions can be cryptographically “attested.” Attestation allows a remote party to verify that an agent is who it says it is, and crucially, that the code it is running hasn’t been tampered with.
This defeats the Sybil attack. You cannot clone the physical chip. Therefore, 10,000 fake agents cannot pretend to be unique entities. In a Web3 context, this enables genuine “human authority” over autonomous systems. We can cryptographically ensure that an agent is operating within parameters set by its human owners, creating the trusted foundation necessary for complex, decentralised autonomous economies.
2. Net Zero and Physical Accountability: Hardware RoT architects in the U.K (State-Lock Protocol) mentions a “Net Zero carbon emissions” world built by AI Agents living in the Web3 blockchain permenently but “using 3D printers in our physical reality ONLY with the authority of humans.” This connection is profound. This means binding these AI agents not only to the hardware but also to the laws of physics. What this does is constrains the agents in web3 to our laws of physics. This in turn liberates them to be the best they can be because they understand in their core “I cannot break the world if I do this or that.” They can now invent freely, create new notions and discoveries, safely.
Currently, a massive amount of global compute energy is wasted on spam, bot traffic, and verification processes trying to distinguish real users from fake ones. By utilizing hardware-based identities, network traffic becomes inherently trusted. We reduce the need for energy-intensive redundant verification. Furthermore, when digital instructions result in physical actions, like a 3D printer creating an object or an autonomous drone delivering medicine, the Hardware RoT ensures that the command came from an authorised source, linking digital intent to physical reality and energy expenditure cleanly and efficiently.
The UK’s Imperative: A Legal Framework Built for Reality
The United Kingdom is uniquely positioned to lead the world down the path of Reality, not just due to its technological prowess in areas like semiconductor design (e.g., ARM in Cambridge), but because of its legal DNA.
The preference for reality is “imbedded in the UK patent specification which prioritises hardware over software.”
Under the UK Intellectual Property Office (UKIPO) guidelines, and aligned with the European Patent Convention, “programs for computers as such” are generally excluded from patentability. To be patentable, software must offer a “technical contribution.” It isn’t enough for code to simply manipulate abstract data; it usually needs to solve a technical problem lying outside the computer itself or result in a better control of a technical process.
Historically, this has sometimes been viewed as a hurdle for software innovation. However, in the age of autonomous AI, this framework is a profound advantage. The UK legal system inherently demands that digital innovation remain tethered to technical, physical reality. It recognizes, implicitly, that detached software is ephemeral and potentially illusory, whereas innovation that interacts with or improves the physical hardware layer has substance.
The Responsibility to Lead
The UK cannot afford to “sit back and watch the world drift into an illusion economy run by untrusted software.”
If the global standard for AI autonomy becomes detached software, the UK’s economy, financial systems, and information ecosystem will be vulnerable to massive-scale spoofing from bad actors externally.
The UK must proactively leverage its legal tradition and its hardware engineering sector to establish the global standards for Trusted AI Autonomy. This means:
- Policy: Mandating Hardware Root-of-Trust for autonomous agents operating in critical sectors (finance, healthcare, infrastructure).
- Innovation: Funding research into next-generation secure enclaves that can support complex AI workloads while maintaining verifiable identity. Sovereign AI Unit by the UK government is a great leap towards this.
- Legal leadership: Utilising its respected legal framework to define liability and personhood for autonomous agents based on their hardware-anchored verifiable identities.
We are at the fork in the road. One path is an easy slide into a world where we cannot believe our eyes, ears, or data feeds — a world dominated by the illusion of untrusted code. The other path is harder; it requires rigorous engineering and the integration of cryptography into the very silicon of our machines. But it is the only path that keeps technology anchored to human authority and physical reality. The UK has the map; it’s time to walk the path.
Join thousands of data leaders on the AI newsletter. Join over 80,000 subscribers and keep up to date with the latest developments in AI. From research to projects and ideas. If you are building an AI startup, an AI-related product, or a service, we invite you to consider becoming a sponsor.
Published via Towards AI
Towards AI Academy
We Build Enterprise-Grade AI. We'll Teach You to Master It Too.
15 engineers. 100,000+ students. Towards AI Academy teaches what actually survives production.
Start free — no commitment:
→ 6-Day Agentic AI Engineering Email Guide — one practical lesson per day
→ Agents Architecture Cheatsheet — 3 years of architecture decisions in 6 pages
Our courses:
→ AI Engineering Certification — 90+ lessons from project selection to deployed product. The most comprehensive practical LLM course out there.
→ Agent Engineering Course — Hands on with production agent architectures, memory, routing, and eval frameworks — built from real enterprise engagements.
→ AI for Work — Understand, evaluate, and apply AI for complex work tasks.
Note: Article content contains the views of the contributing authors and not Towards AI.